In recent years, the internet has grown into a complex digital landscape—vast, borderless, and filled with extraordinary opportunities. Yet beneath its surface lies another world entirely: a network of hidden platforms, encrypted communication systems, and secret online communities that operate in the shadows. For years, many of these groups were believed to be nearly impossible to track, slipping between jurisdictions and hiding behind advanced technology. But a groundbreaking international investigation has now revealed just how far modern law enforcement has come.
What began as a small anomaly noticed by cyber analysts eventually led to one of the most extensive global criminal takedowns ever attempted. The operation—coordinated by federal agencies in the United States and supported by partners in more than 30 countries—exposed underground networks that operated like full-scale criminal enterprises. These weren’t casual online forums or isolated bad actors. They were structured organizations with layered hierarchies, sophisticated security systems, and members scattered across hundreds of cities worldwide.
Through years of undercover work, digital forensics, financial tracing, and collaboration with foreign governments, investigators were finally able to identify key operators and dismantle the network from the inside out. The result was a wave of arrests across multiple continents, the seizure of servers and encrypted devices, and the exposure of previously unknown criminal hubs hiding in plain sight beneath layers of coded software.
What follows is an in-depth look at how this unprecedented operation unfolded, how investigators cracked systems once considered unbreakable, and how this case is reshaping future strategies for fighting cybercrime.
The Digital Footprint That Sparked the Investigation
The origins of the investigation were surprisingly small. A group of analysts monitoring unusual activity patterns on hidden servers noticed behavior that didn’t fit the typical profiles of decentralized online communities. The traffic spikes were irregular, the encryption layers far more advanced than normal, and the communication behavior suggested a strict internal structure rather than casual conversation.
Working quietly, analysts traced various digital threads—subtle login behaviors, encrypted metadata fragments, and financial patterns involving small cryptocurrency transactions that didn’t align with any legitimate purpose. Over time, these anomalies connected to one another, revealing the early outline of something much larger.
At this early stage, the data was fragmented and incomplete, but one detail stood out: the patterns suggested thousands of users operating within an unofficial closed network, accessible only through specialized software and protected by multiple authentication layers. That level of secrecy typically signals organized criminal activity, prompting investigators to launch a discreet inquiry.
A Hidden Network Functioning Like a Criminal Corporation
When federal officials finally gained partial access to the platforms, they discovered something far more organized than expected. These digital spaces operated with the precision of corporate ecosystems. Members followed structured rules, a ranking system determined privileges, and moderators enforced strict operational guidelines. There were even training documents—guides written to teach newcomers how to avoid detection by authorities, how to encrypt their communications, and how to erase digital footprints.
Communication took place on multi-layered encrypted channels, often routed through servers located in countries with minimal digital oversight. Cryptocurrency wallets were used to mask the movement of funds, with money passing through mixers, tumblers, and international accounts in an attempt to make tracing nearly impossible.
This was not the work of random individuals. It was an international organization with a clearly defined operating model.
Building the Task Force: The Birth of Operation Grayskull
Recognizing the scale of what they had uncovered, federal officials launched what would become a landmark collaboration—Operation Grayskull. Over the next several years, experts from the FBI’s Cyber Division, Homeland Security Investigations, Europol, and numerous national agencies across Europe, Asia, Australia, and South America joined forces.
Teams of digital forensic specialists analyzed seized files, traced online identities, infiltrated chat systems, and mapped out the network’s internal hierarchy. Undercover operatives posed as participants, gathering intelligence from within. Meanwhile, financial analysts worked to decrypt and reconstruct the currency trail flowing through cryptocurrency networks.
Cooperation was essential. No single agency could have pursued all the leads alone, especially with perpetrators scattered across dozens of jurisdictions. The operation required synchronization at every level—legal, technical, and physical.
One federal official noted that without international support, “The entire system would have simply migrated to another server before we could make a single arrest.”
Infiltrating the Encrypted System
Gaining access to the core of these platforms was one of the operation’s greatest challenges. The network used an advanced combination of Tor-based routing, passphrase-protected entry portals, and custom encryption algorithms. Even if investigators breached an outer layer, they often encountered dead ends—fake pages, decoy accounts, or time-limited access keys designed to self-delete after a single use.
Cyber specialists eventually identified a vulnerability in one of the authentication layers. It was a flaw so minor that even the network’s administrators had overlooked it. Using that vulnerability, investigators slowly extracted useful fragments—small pieces of data that, when assembled, built a partial roadmap of user activity.
The breakthrough allowed officials to link real-world devices to seemingly anonymous accounts. Once agents had those links, they began compiling dossiers on suspects worldwide, monitoring online behavior while preserving secrecy to avoid tipping off the network.
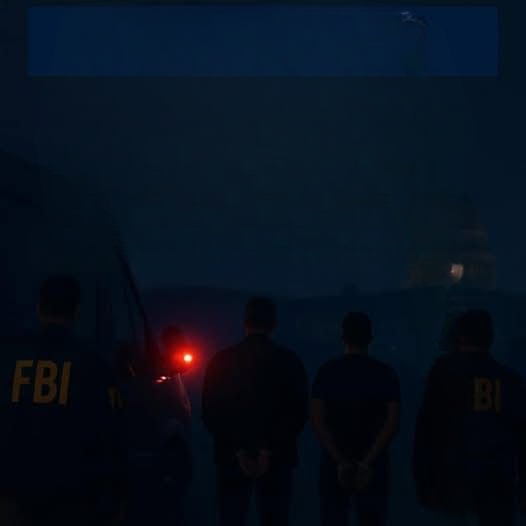
Coordinated Raids Across the Globe
When law enforcement finally moved, they did so with precision. Raids were launched almost simultaneously across multiple nations to prevent suspects from destroying evidence or warning one another.
In Germany, officers discovered a warehouse that had been converted into a massive server hub. Hundreds of machines were stacked in rows, many running specialized software used to mask identities and facilitate communication within the secret network.
In Australia, investigators seized encrypted laptops and storage devices from a suburban home. The devices contained thousands of messages between mid-level members coordinating logistics and discussing updates to their evasion strategies.
In the United States, multiple arrests were made across different states, including individuals involved in managing server infrastructure, moderating online channels, or distributing software tools used by the organization.
The amount of seized digital evidence was staggering. Officials described entire storage rooms filled with devices awaiting forensic analysis.
Inside the Sentencing: What the Courts Revealed
As the cases progressed, prosecutors highlighted the severity of the criminal organization’s structure and the extensive harm it caused. Several defendants held roles similar to corporate administrators—handling user management, ensuring platform stability, or overseeing communication systems.
Sentences were severe:
-
One defendant received 20 years for actively participating in the distribution of illegal materials and encouraging further wrongdoing.
-
Another individual in a separate case was sentenced to 55 years after evidence showed a direct role in producing content that led to the exploitation of minors.
-
Several moderators—individuals responsible for approving and organizing illegal activity—received sentences ranging from 23 years to life.
Federal attorneys emphasized that these penalties reflect the gravity of crimes committed on a massive scale, impacting victims across numerous countries.
One Justice Department representative stated:
“These networks were not informal or opportunistic. They were organized, deliberate, and extraordinarily harmful. The sentences reflect society’s demand for justice.”
Rescuing Victims and Rebuilding Lives
One of the most profound outcomes of Operation Grayskull was the identification and rescue of victims. Digital forensic teams painstakingly analyzed images, backgrounds, audio fragments, and embedded metadata from seized files. These details offered clues—objects in a room, labels on supplies, environmental sounds, or even the types of devices used.
Through this careful work, dozens of children across the United States, Europe, and Asia were located and removed from harmful environments. Many were taken into protective custody and connected with support organizations trained in trauma recovery.
Advocacy groups praised the operation not only for capturing perpetrators but for bringing hope to survivors.
The Technology Behind the Takedown
Operation Grayskull showcased how modern digital forensics has evolved. Investigators used:
• Blockchain Analysis Tools
To track cryptocurrency transactions that had been routed through multiple accounts.
• Metadata Reconstruction
Allowing specialists to rebuild deleted or encrypted information.
• Machine Learning Models
To identify patterns in communication behavior that pointed toward leadership roles within the network.
• Undercover Digital Personae
Sophisticated online identities capable of interacting with perpetrators without revealing law enforcement presence.
Authorities stressed that these technological breakthroughs represent a new era in cybercrime investigations.
Why International Collaboration Was Essential
One of the biggest obstacles in cybercrime investigations is jurisdiction. Offenders often distribute servers, accounts, and transactions across multiple countries, making prosecution difficult.
Operation Grayskull overcame this challenge through unprecedented cooperation:
-
Europol coordinated intelligence sharing.
-
German and UK law enforcement conducted simultaneous raids.
-
South Korean authorities tracked financial transactions.
-
Australian teams located secondary servers and communication devices.
Officials emphasized that the operation’s success sends an important message: no country is isolated when confronting global cybercrime, and criminals can no longer assume they are safe simply because they hide behind borders.
Public Reaction: A Mix of Shock and Relief
When the details of the takedown were made public, the response was immediate. Advocacy groups praised investigators for their dedication, recognizing that many specialists spent years reviewing deeply troubling digital material in order to build the cases.
Technology experts commended the operation for exposing vulnerabilities in systems previously believed to be impenetrable. Meanwhile, families and communities expressed gratitude that so many victims had been identified and rescued.
However, cybersecurity professionals also warned that the fight is far from over. Hidden networks are adaptive—they rebuild, relocate, and adopt new techniques. Every takedown reduces harm, but new threats inevitably emerge.
The Ongoing Battle Against Online Exploitation
Officials made it clear that despite the enormous scale of Operation Grayskull, the work is ongoing. The dark web continues to evolve, and encrypted communication tools grow more sophisticated every year.
But the operation changed the landscape in several key ways:
-
It proved that even the most advanced networks can be infiltrated.
-
It exposed the international coordination behind cybercriminal communities.
-
It strengthened partnerships between agencies worldwide.
-
It provided invaluable intelligence that will fuel future cases.
As one senior FBI agent summarized:
“The internet is vast, but it is not lawless. Anyone who believes technology can shield them from accountability is gravely mistaken.”
A Landmark Victory, but Not a Final One
Operation Grayskull stands as one of the most significant global cybercrime takedowns to date. It dismantled major networks, rescued victims, and brought high-ranking offenders to justice. Yet investigators emphasized that this is only one step in a long-term effort to protect vulnerable individuals and ensure that criminals cannot use digital anonymity as a shield.
Moving forward, authorities plan to expand intelligence-sharing networks, adopt more advanced forensic tools, and work even more closely with private technology companies to create safer online environments.
The message is clear:
No matter how hidden, encrypted, or global the operation, justice will find its way in.